Windows Users Beware: Missing BitLocker Recovery Key + Corrupt Windows = Bad News
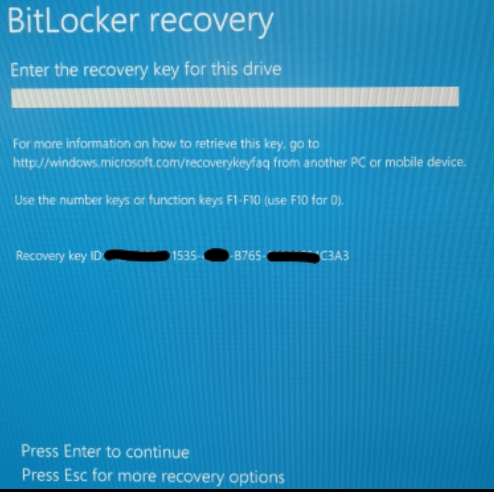
What happens when you have BitLocker enabled and your Windows installation becomes corrupt, leaving you no longer able to boot into Windows? Normally you would go into Recovery Mode. The device asks you for your BitLocker recovery key which, if you hadn’t written it down, you can find by looking in your Windows Account under the Devices section.
But what do you do if it isn’t there? And how can you be missing a recovery key if it’s safely stored on Microsoft’s servers?
What Happened?
Our client originally had an email address with his ISP that they had used to sign up for a Windows Account. At some point in time, they signed up for an Outlook email address. They then edited the associated email address with their Windows Account to be their new Outlook address.
All was still well for them at this time. Later on, the client bought a new laptop and enabled BitLocker on it. Unfortunately, after setting up the new laptop, their Surface Pro 3 entered a boot loop and would not boot into Windows anymore. More specifically, Windows started to boot but crashed and restarted in Recovery Mode.
Where Was the BitLocker Recovery Key?
This is where it gets interesting. The client logged into their Windows Account and went to the Devices section only to discover that the Surface Pro 3 was not showing in the Devices section. The newer laptop they bought (provisioned with the Outlook.com email) did appear in the Devices section, however. So with that in mind, the client switched the assigned email in their account back to their previous address. They hoped this action would reverse the issue. However, still, no recovery key showed up in their Devices Section.
One can only assume that the recovery key was originally in the Devices section for the Surface Pro 3. However, assigning a different email address to the client’s Microsoft Account had not carried over the device’s recovery key. Worst of all, reverting the assigned email back did not reverse the issue.
What Can Microsoft Do About This BitLocker Recovery Bug?
Our client said that they were not able to get any help from Microsoft support on the phone. Instead, Microsoft simply told them to reformat and start anew. Obviously, reformatting was not an option. Their data lived in the broken Windows installation currently held hostage by BitLocker.
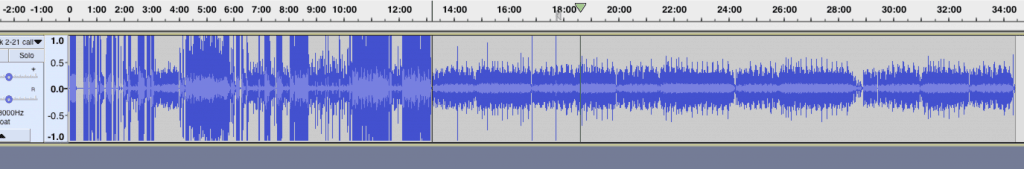
We reached out to Microsoft as well via the Windows team and the Surface team. We were met with constant phone transfers and periods of long holds. You can see clearly in the following image which parts of the call we spent on hold:
A second call we made assured us that we could find the key would in onedrive.live.recoverykey, even though it would not show up in their Microsoft Account – Devices section. After logging in and checking this was found to not be the case as well.
A third and final attempt, after following their instructions, just led to “thanks for calling Microsoft, goodbye.”
This possible bug may be affecting thousands of other Microsoft customers. Hopefully, Microsoft will take meaningful steps to rectify this bug so that end users do not irrevocably lose access to their data like this.
What Could Gillware Do About It?
What is a TPM?
A TPM (Trusted Platform Module) is a specialized chip designed for an extra layer of encryption protection. The TPM is what actually stores the volume master key for the device. The sole purpose of the TPM is to ensure that nothing about the device’s environment, such as the OS or hardware, has changed. As a result, the only way to access the data on the device is by booting into Windows and logging on with the correct credentials. This helps prevent any unwarranted software/people/hardware from accessing the device and the data stored within.
There Are No Locksmiths for Encryption
If the TPM detects a change in its environment, it won’t release the volume master key. Recovery mode, which the Surface tablet tried to start up using, is not the same OS as Windows, so the TPM would not unlock the device. In addition to this, disabling automatic recovery mode would also count as a configuration change.
No matter what avenue our engineers ventured down, including using the Windows Recovery software from Microsoft themselves, we were dead in the water without the BitLocker Recovery Key. As a result, our engineers could not access the device and its contents through any method.
When you end up locked out of your house because you lost your key, you can call a locksmith. You can have your landlord order a copy of your lost key. When you end up locked out of your data because you lost your password, there’s no locksmith on Earth who can help.
When encryption enters the fray, there are some things even Gillware cannot do. Full device encryption works. It works whether you want it to or not. It works especially when you don’t want it to, rendering your data ultimately inaccessible should you lose the password or other credentials. Make sure to always keep your passwords in a place where you will not lose them.
Data Recovery Software to recover
lost or deleted data on Windows
If you’ve lost or deleted any crucial files or folders from your PC, hard disk drive, or USB drive and need to recover it instantly, try our recommended data recovery tool.
Retrieve deleted or lost documents, videos, email files, photos, and more
Restore data from PCs, laptops, HDDs, SSDs, USB drives, etc.
Recover data lost due to deletion, formatting, or corruption
A Bug With No Resolution
Before they came to us, our client spent a lot of time and effort trying to reach Microsoft to find a resolution to this BitLocker Recovery issue to no avail. Due to the efficacy of data encryption, there was nothing Gillware could do without the password either. This bug represents a serious issue that could affect thousands of users.
Hopefully, in the future, Microsoft will be aware enough of this issue with disappearing BitLocker recovery keys in users’ Windows Accounts to do something about it.
Until then, be forewarned:
Altering the email address tied to your Windows Account could result in critical data irretrievably disappearing from your account. Store your recovery key and other passwords in multiple safe locations, such as a secure password manager or safety deposit box. These measures will help you avoid getting locked out of your data.
BitLocker Recovery Loop
It’s possible that even if you have the correct recovery key, you’re still unable to log in to your computer after a crash. This is a known issue referred to as a recovery loop. When a BitLocker recovery loop occurs, the Windows user is unable to access their operating system despite entering the correct BitLocker recovery key. This phenomenon can be very frustrating. Gillware data recovery engineers have experience restoring data in the event of a BitLocker recovery loop.
Need help getting your data back?
When you don’t know where else to turn, turn to Gillware. We will provide a free in-lab evaluation of your device and let you know what we can recover from it.

