Encrypted Data Recovery: The Case Study That Destroyed Humanity
Recently, a potential client contacted us, wondering if we could recover data from their Apricorn Aegis Secure Key 3.0 USB drive. The USB flash drive itself was in perfect condition. However, the data was inaccessible because the device was password-protected with 256-bit AES encryption—and the user had forgotten the password. Furthermore, the device had a protection against “brute-force” guessing the password—10 incorrect password entries would completely wipe the device, erasing all of its contents. The user wanted to know if we could perform encrypted data recovery without knowing the password to the device.

At Gillware, we deal with encrypted data recovery cases all the time. We deal with everything from SmartWare and FileVault encryption to PGP and EFS encryption. Recovering data from encrypted storage devices takes a few extra steps compared to recovering unencrypted data, but as long as we have access to our client’s proper credentials, the process usually goes fairly smoothly (although it can take a bit longer).
But as we’ll explain in this encrypted data recovery case study, data recovery is only really feasible when we know the password to decrypt the data.
Is Encrypted Data Recovery Possible Without a Password?
To make a long story short, no, encrypted data recovery is impossible without the password.
To make a long story long, it is possible—but only theoretically. And here we mean theoretically in the same sense that, according to all known laws of cosmology, diving head-first into a very specific type of black hole can theoretically plunge you into an alternate universe. (But you’re more likely to be torn apart in a process scientists like to call “spaghettification”—and while the name may suggest otherwise, it is not a delicious way to die at all.)
Possible? Theoretically, yes.
Plausible? Not in a billion years (and we mean that quite literally).
In other words, don’t count on a trip to Cygnus X-1 to be your gateway to a better universe.
But let’s walk through the steps that data recovery experts would have to take to recover encrypted data without a password, just for fun.
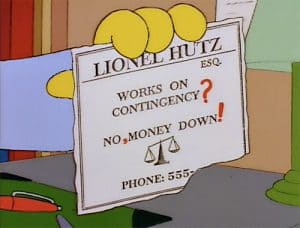
Encrypted Data Recovery—No, Password Needed!
For starters, let’s look at the situation. When you encrypt or decrypt data, you use an encryption key. This key has a set number of randomly-generated bits. The more bits in the key, the harder it is to “guess” the key and decrypt the data.
256-bit AES encryption means you would need to guess up to 2256 times (that’s two multiplied by itself 256 times, which roughly translates to 115 quattuorvigintillion, where a quattuorvigintillion is a one followed by 76 zeroes) to correctly figure out the key.
To put into perspective how big a number that is, the US national debt as of January 2016 was $13.6 trillion, and a quattuorvigintillion is like if a trillion multiplied itself by itself 25 times in a row.
The key is randomly generated, but your password is not. When you create a password, you tie that password to the key itself so that when you put in the correct password (and only the correct password) the device recognizes it and decrypts your data.
The password is potentially much simpler to figure out than the key. Most devices tend to have an upper limit of how long a password can be—say, 32 alphanumeric characters, for example—and a limit on what kinds of characters it can contain. Now, this still comes out to a ridiculous amount of possible passwords to guess (although not a quattuorvigintillion of them). If we’re lucky, we might only need to guess half the possible combinations before hitting the right one! (We’re assuming the user was prudent and designed a hard-to-guess password that would rule out common approaches to password guessing.)
But, of course, we can’t exhaust all of the possibilities—because this Apricorn Aegis flash drive has a 10-guess limit. If you guess incorrectly ten consecutive times—you lose.
A Theoretical Encrypted Data Recovery “Hack”
There’s one way around that ten-guess limit. But it takes a lot of hard work. First, our flash memory engineers would disassemble the flash drive and remove its NAND chip (or chips). Then, we would copy and back up all of the raw data on the chips. Then we would reassemble the flash drive.
With flash drive’s “baseline” state backed up, we’d make our ten guesses. Our chances of actually guessing the right password right off the bat here would be slim to none, though. And after ten unsuccessful attempts, we’d go back to the drawing board.
To get our next ten guesses, we’d rinse and repeat. Remove the NAND chips again, write the images we’d made back to the chips to restore them, reassemble the flash drive, and make our next ten guesses. We’d be doing a chip-off data recovery… over and over and over again.
Each chip-off attempt would take about four hours (safely removing flash memory chips is hard work)! About one thousand dollars worth of labor from our flash memory data recovery experts would go into each attempt. Let’s look at a cost and man-hours breakdown of this approach:
The Data Recovery Case That Destroyed Human Civilization
Assuming we don’t get the right password until we’ve eliminated every other possible combination, and the password is as complex as the encryption key itself, we would have to repeat this four-hour, thousand-dollar procedure 2255 times. That’s over 5.7×1076, or 57 quattuorvigintillion chip-offs.
Of course, we might discover the right password after exhausting half of all the possible passwords, or a quarter, or a tenth, or even a fraction of a fraction of a fraction of a percentage of the possible passwords. The password would likely be very simple compared to the key, and we might even get it within a couple million attempts, especially if we use a dictionary attack to guess more likely passwords first. But even then, that’s still a mind-boggling amount of attempts to go through.
Multiply that by four to get the maximum man-hours this job would take. Multiply it by 1,000 to get the baseline cost for the data recovery work.
In many cases, the time expenditure alone would vastly exceed the current age of the universe and probably the projected lifespan of the universe as well. The monetary cost would force the entire human race into debt slavery for about as long of a time frame. Your children’s childrens’ children’s… (repeat for a couple trillion trillion times)… children would be toiling well after the heat death of the universe to foot the bill for this case.
Unimaginable aeons have passed. The universe is a dark and empty place. There are no more stars or planets. Heavier elements can no longer form. Even black holes begin to vanish into oblivion. And this data recovery case still isn’t finished yet.
You might now truly grasp the idea that, yes, modern encryption is very, very, very powerful.
Encrypted Data Recovery: A Slightly Less Implausible Shortcut
We here at Gillware would rather not potentially consume the entire productive capacity of the human race until the end of time itself to brute-force a password. Fortunately, there is another way.
We could go to Apricorn themselves, or the designers of the controller used in their secure USB drives, find the guy who wrote the code for the security features, and try to get at the source code and comment out the bits about the ten-guess password limit. Then we’d plug in the images we made of the raw NAND chip data, and start our guessing uninhibited.
Of course, we’d still have to guess just as many times, but each attempt would take substantially less time. We’d start with a dictionary attack, and hopefully get the password within the first few million attempts.
However, the chances of Apricorn (or really any reputable manufacturer) willingly giving up their own source code would not be slim to none—they would be nonexistent. We would be asking Apricorn to intentionally cripple their own security product! They would never agree to such a thing. The universe-ending, humanity-enslaving approach we’ve outlined above would probably have a better chance of success!
Realistically, what we would do is try to reverse-engineer the USB drive’s firmware and edit the portion that limits us to ten guesses. This would take months upon months of R&D time, a lot of blood, sweat, and tears, and might not yield any positive results at all. And then, of course, we still have to do all the guessing. The price tag would be well into six-figure territory.
All things considered, the data on the USB drive would have to be very important to warrant such expenditures.
The Key to Encrypted Data Recovery
Hopefully we’ve laid out just how hard and time-consuming it could be to brute-force the password on one of these Apricorn Aegis Security Key 3.0 USB drives. 256-bit encryption is very serious about what it does. If it were easy to break encryption, there’d be no point in encrypting anything!
When hackers break into a user’s account or device, they usually do so not by brute-force guessing the password, but through other kinds of trickery. A keylogger virus can send the data about what you type in to your computer to them, including login credentials for various services. Hackers often use phishing schemes, such as sending people to fake login pages for services like Google Drive and Dropbox, to get them to unwittingly hand over their login credentials.
But when hackers do try to brute-force a password, they do so in the hopes that their victim is one of the many people who use simple, easy-to-remember (and guess) passwords. A password that involves your name, your pet’s name, your company’s name, your mother’s maiden name, the street where you grew up on, your birthdate, etc. is much easier to hack than a truly randomly-generated password. A hacker can easily get this kind of information just by stalking you on social media (or a genealogy website…). Passwords like these can take only a couple thousand or million tries to guess, rather than the trillions, quadrillions, or quattuorvigintillions of guesses a stronger password might require. Using real words or combinations of real words is a no-no in password creation.
Encryption doesn’t fool around, so don’t be surprised when the ultra-secure storage device you’ve purchased works exactly as intended. A proper, strong password is all but unbreakable.
Forgot Your Password? Here’s the Best Encrypted Data Recovery Method
If you’ve forgotten the password to your encrypted hard drive or thumb drive, unfortunately, even the world’s top encrypted data recovery experts won’t be able to help you.
You can find a much cheaper, quicker, and potentially more effective solution—a hypnotist. A professional hypnotherapist may be able to help you recall that password you’ve forgotten. However, so-called “recovered-memory techniques” are all still rather controversial and currently lack hard evidence of their efficacy.
All in all, the key to encrypted data recovery is your password. Keep it secret. Keep it safe. But make sure you write it down somewhere…
