Recovering a Legend: Technical Details of Recovering Robert Goulet’s Legacy
Mr. Goulet may be gone, but the impressive legacy of his work was safe.
Recently, we completed a data recovery for Vera Goulet, wife of the late Robert Goulet. Our Director of Research and Development, Greg Andrzejewski handled the case. In this post, he gives us some insight into the technical details of what it took to recover the lost data.
Years ago, you could crack open any external USB hard drive and you’d find an ordinary SATA hard drive and a small PCB containing a USB-SATA bridge chip. As its name implies, the bridge chip acts as a go-between for a PC “speaking” USB and a hard drive that only understands SATA. Most operate in a relatively straightforward manner; USB commands are simply translated to their SATA equivalents and the same data is written to the same location as if the drive were directly attached to the motherboard. From a recovery standpoint, the fact that the drive is an external is irrelevant; the HDD can be removed from the enclosure and processed as if it were a plain old SATA drive. The drive itself is usually the problem anyway and direct SATA access is the most effective way to address most issues.
Nowadays, crack open an external USB drive and you’re likely to find what looks to be just a native-USB hard drive. This was, indeed, what we found with Mrs. Goulet’s external. Closer inspection, however, will reveal a USB-SATA bridge chip integrated on the drive PCB. Functionally, nothing’s different; it’s still a SATA hard drive connected through a USB-SATA bridge. Practically, though, getting direct SATA access to the drive is no longer as simple as removing the drive from the enclosure. Instead, the SATA signals must be “tapped” from traces on the PCB, intercepted as they travel from the drive controller to the bridge.
Another increasingly common feature of external USB drives is built-in hardware encryption. With these drives, the USB-SATA bridge chip not only acts as an interpreter but also as a gatekeeper. Instead of simply passing data straight through to the drive, the bridge first encrypts the data with an AES cipher. Drives removed from from these types of enclosures appear to contain gibberish when directly connected. A quick inspection of key areas on the disk coupled with the known capabilities of the specific bridge chip confirmed that anything read directly through our tapped SATA port would not be directly usable.
In some situations, we are comfortable removing our SATA tap after making adjustments and letting the bridge chip work its magic, decrypting the drive on-the-fly as we image it over USB.
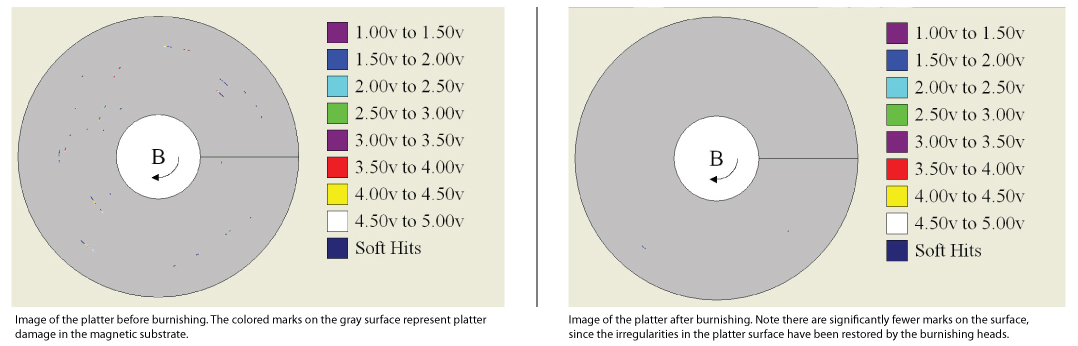
Our routine inspection of the drive’s internal mechanics, though, revealed a significant amount of platter damage. With drives in this condition, sometimes you only get one shot at recovery. Platter damage can spread quickly, so we thought it best to grab data while we could, even if what we’re reading is fully encrypted.
The platters, of course, are the thin glass or aluminum discs inside the sealed hard drive enclosure. Each surface is coated with a thin magnetic substrate that retains data in the form of a magnetic field. Data is accessed by positioning a tiny sensor called a read/write head over the magnetic surface as it rotates at thousands of rotations per minute beneath it. The platter surface is pristine and, when combined with the high rotation rate, creates a cushion of air for the read/write heads to ride upon as they navigate the platter.
However, in certain situations the heads can “crash” and contact the delicate platter surface, damaging the layer of substrate and spreading microscopic debris throughout the chassis. Though this damage may seem minor, the debris continually impacts the read/write heads, eventually destroying them and rendering the drive inoperable.
The solution seems simple; just replace the failed read/write heads. In order to achieve such high storage densities, though, modern hard drives are intricately calibrated at the factory to the specific characteristics of their read/write heads. Getting a drive to accept a replacement read/write head stack is no easy task. Furthermore, the new read/write heads are no less susceptible to the sort of damage that caused the original set to fail.
The real issue that must be addressed is the damage itself. As long as debris still litters the platter surface, the drive will continue to destroy head stack after head stack and spread damage to other areas of the drive. Drive manufacturers are well aware of this fact and use sophisticated equipment in the factory to measure and eliminate platter imperfections. At Gillware, we use the exact same tools as the factory, albeit re-engineered to meet the needs of recovery.
The process of removing platter imperfections is known as burnishing. The first step, as you might imagine, is removing the platters from the drive chassis. The platter is mounted on a custom fixture that spins the platter in excess of 10,000 RPM. A robotic arm then passes a specially designed burnishing head over the platter. Think of the burnishing head like a very precise scrub brush, sweeping up debris as it passes over the platter surface. Depending on the severity of damage, the burnish process can take anywhere from a couple minutes to many hours. After burnishing all the surfaces, the platters are remounted in the drive chassis and new read/write heads are installed and calibrated.
While the drive is by no means perfect at this point, it will operate will enough to extract the data from the device. If there are areas of extreme damage on the platters, data may be lost permanently, but in this case we were able to extract all of the data we were after, albeit still encrypted.
The decryption key is actually stored on the drive itself, in an area hidden from the user by the USB-SATA bridge chip. We held our breath as we directed our imaging software to this area, knowing that, at most, there are just two copies of a piece of information, that without, recovery is impossible. Software-based encryption products practically force you to make a backup copy of the decryption key should disaster strike. Manufacturers of hardware self-encrypting storage devices do not even allow this (most see the inaccessibility of the decryption key as a “feature”. A sigh of relief echoed through the lab as the drive produced the keys to the kingdom. Mr. Goulet may be gone, but this impressive legacy of his work was safe.