Case Study: Panasonic KX-TG4741 Deleted Voicemails
Recovery Type: Answering Machine
Internal Memory: 2MB
Manufacturer: Panasonic
Model Name: KX-TG4741
Manufacture Date: 11/2011
Main Symptom: Deleted Data
Type of Data: Voicemails
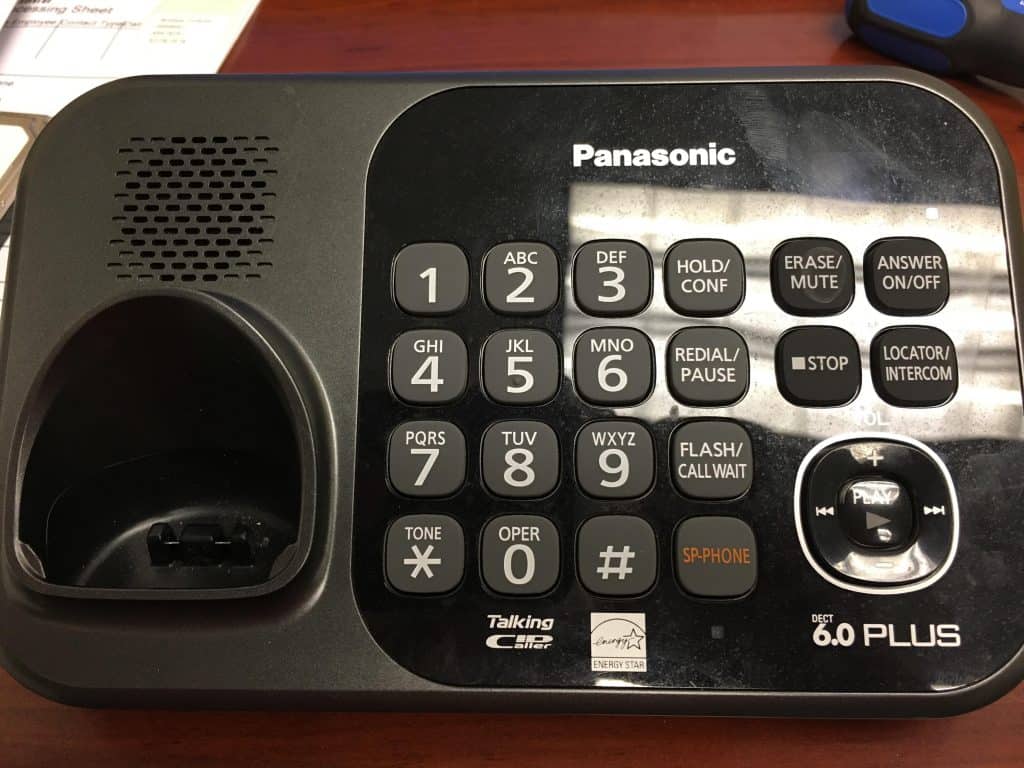
Background: This is a unique case study as Gillware has never received a recovery case for an answering machine before this. We have received mobile phones with voicemails, (non-phone) sound recorders, surveillance cameras, and of course all the typical fare, but never an answering machine. It’s likely that nearly all our competitors would have refused this case, but Gillware is fortunate to have some fantastic people who are willing to reverse engineer just about anything that holds data. The client was hoping to retrieve some deleted voicemails from the system, so after some short questions our recovery team set to work.
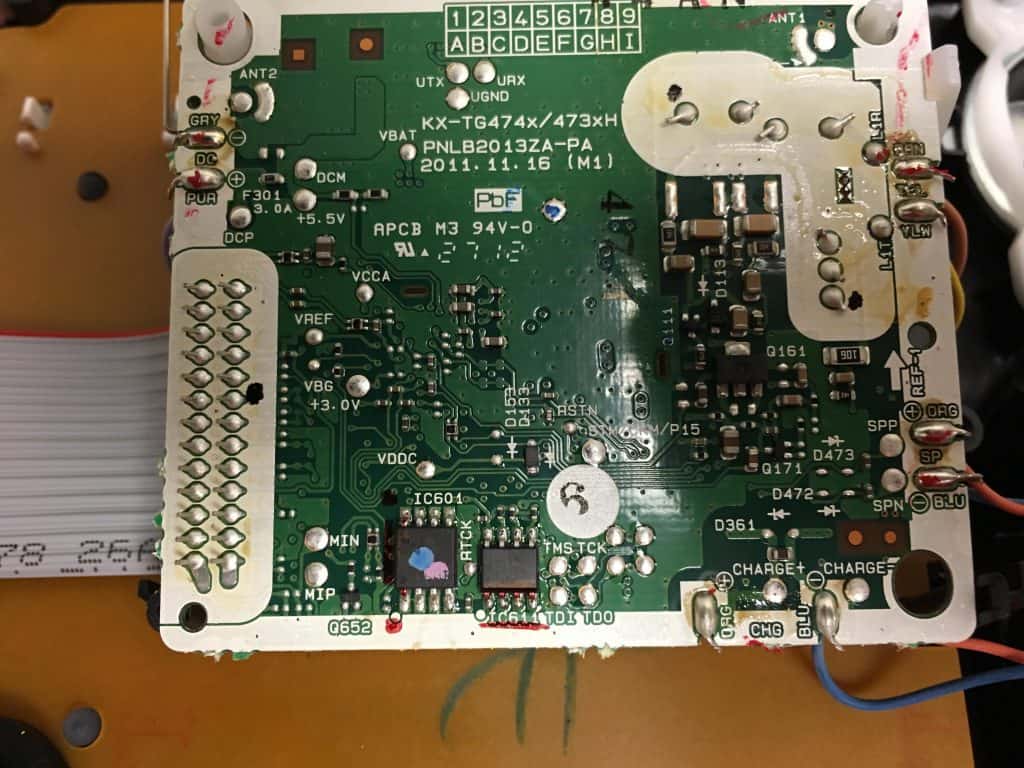
Evaluation: Similar to other cases, we bought the same exact machine from the Internet so we could study it without concern of damaging the client’s model. After taking it apart, our engineers discovered it used electronic NVRAM instead of a tape system.
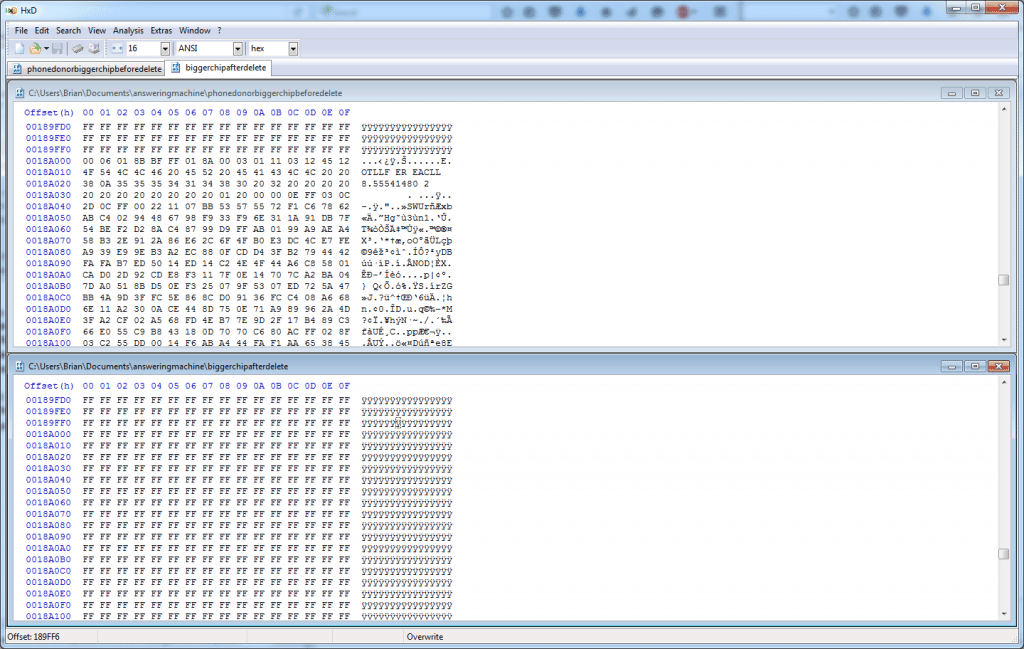
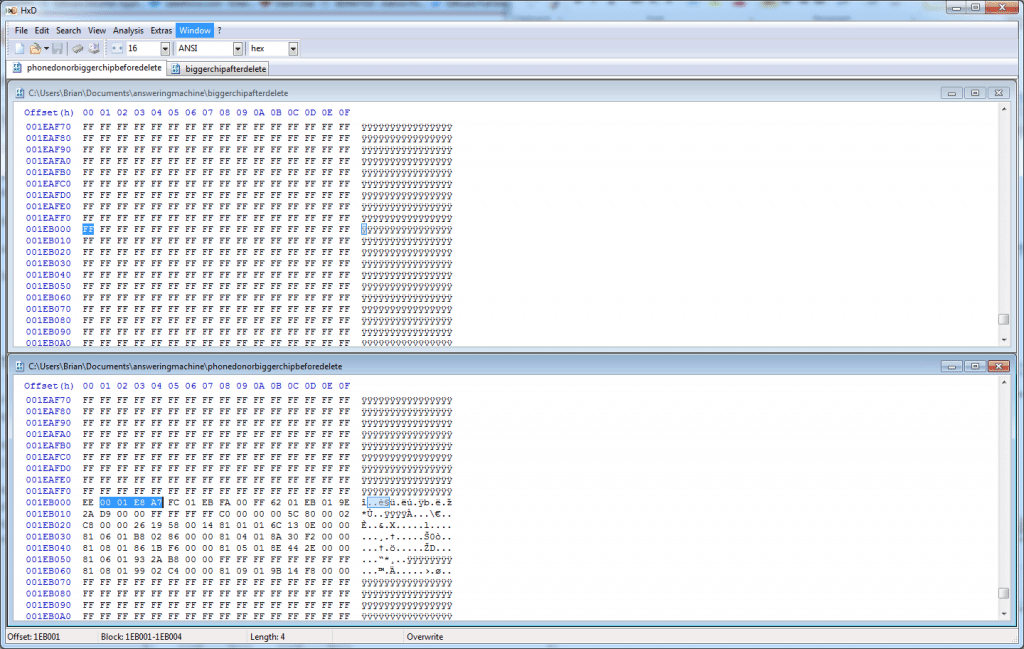
Recovery: The Internet-bought machine already had a few messages on it, so we took the storage chips off and examined them. The first was only 8KB, and based on this we assumed it wouldn’t be large enough to store any audio recordings. The second chip was 2MB and was where the audio files were stored. Since there were already a couple messages on the test system, our engineers decided to put the chips back on and then delete a message as a means of discovering what the system does with deleted files. Modern file systems typically save write operations and make small changes to the file system metadata to unallocate the space and alter the inode/dirent. Unfortunately, it was discovered that this particular unit permanently wipes the call by filling the space with 0xFF. To clarify, “FF” is just the placeholder value that is used to overwrite all the data for the message, so instead of seeing a bunch of different hex values where the message lives, they all just become FF and the message is lost forever.
From one of our engineers on above pic: “This is the hex of a recorded call from caller ID ‘TOLL FREE CALLER.’ After the header, the voice stream follows. Here is where you can see it fills the unallocated space with hex 0xFF. The entire call lived from 0x18A000 to 0x18D200.”
From the same engineer on above pic: “This is the call header that was basically an index into where the message lived within the chip. I’ve highlighted the addressing of the stream. As you can see it was also FF filled on deleted.”
Results: Despite a valiant attempt by our recovery engineers, it was discovered that it is impossible to recover any deleted data from these types of answering machines. Since the unit completely overwrites the sectors with 0xFF and there is no way to rewind bytes once they’re overwritten, the previous data is gone forever. Since we weren’t able to recover anything from the answering machine, the customer was not charged for the recovery. We don’t typically post case studies for failed recovery attempts, but this one seemed interesting enough to warrant a write-up. It is unlikely we will ever encounter another case like it, but at least we know what to expect in the future if we do.
