Digital Forensics for Blackberry Devices
Experienced examiners can often determine who someone talked to and when, where they went and where they were going, which applications they used and a whole host of other things. Even in tricky situations where the Blackberry device is not able to be accessed due to security settings and the application of a passcode, there may be ways to obtain evidence from these devices. Experienced examiners can also be used to clearly communicate this evidence to a court of law.
BlackBerry Overview
BlackBerry devices first came on the tech scene in 1996 with the release of the inter@active pager 900, a device that allowed two-way paging. Over the years they advanced to become a major player in the smartphone market, reaching their peak in late 2012/early 2013 with over 80 million global users. Unfortunately, this success did not last and as of 2016 they are down to around 20 million users, a fraction of their former glory.
Older BlackBerry devices ran on a proprietary OS known as BlackBerry OS until 2013, when an updated version based on the QNX operating system was released and named BlackBerry 10. This new operating system was meant to focus more on the UX of modern smartphones rather than the security and productivity that BlackBerry had been known for in the past. Interestingly, 2015 saw another OS shift for BlackBerry devices when they decided to release Android-based smartphones. For the purpose of cleaner categorization, those smartphones will not be included in this page, as we have a separate page for Android Forensics Services.
With different operating systems and different styles of smartphones, some with keyboards and some with full touchscreens, there’s a bit of variety with BlackBerry devices. Devices running BlackBerry OS versions prior to 10 run on a J2ME platform with apps created in Java using Research In Motion (RIM) custom APIs. For security purposes, apps have a limited amount of access to memory and are run in a “sandboxed” environment. Apps only have access to their own data, not that of other apps or the OS.
For models released between 2013 and 2015, these devices feature the improved BlackBerry 10 operating system. Most of the improvements here have to do with basic features you might find on most other smartphones, such as improved user interface, voice recognition software, video chat, flash for web browsing, and more.
One feature that is particularly relevant to BlackBerry forensics work is the application known as “BlackBerry Protect,” which is featured in both the newer and older operating systems. This application is similar to the “FindMyiPhone” feature you find on iOS devices and is used to help remotely back up, locate, lock, and even wipe the data from a lost or stolen device. This obviously has huge ramifications for securing devices for BlackBerry forensics work. As with other smartphone devices, it is considered a best practice to isolate them from any outside signals by turning off Wi-Fi and Bluetooth, removing the SIM card, and more.
What Services Does Gillware Offer for BlackBerry Forensics?
Cindy Murphy, president of Gillware Digital Forensics, has a lot of experience performing forensics work on BlackBerry devices. With her many years as a digital forensics expert working for the Madison Police Department, she brings unparalleled expertise to the Gillware team and allows us to work on some very interesting and difficult cases. Along with our world-class data recovery team with over a decade of experience, there are few BlackBerry device situations that we can’t perform forensics work on. This includes logical device issues, physical device issues (broken) and more. Whether it’s for law enforcement, legal professionals, corporations, or more, we can assist with the case.
One difficult situation that we encounter, similar to with iOS devices, is that the passcode is often necessary in order to acquire the device, meaning access and dump all the data contained within the device. This holds true for both older models on BlackBerry OS and newer models running BlackBerry 10. Although this can make a case more difficult, there are still a few things that forensic examiners might be able to do to work around this.
Recovering Data from Broken BlackBerry Devices
We recover data from broken BlackBerry devices in situations where many organizations might not be able to. Our experience working on complex cases has led to developing industry-leading techniques for working on broken devices, whether the damage is from fire, water, blunt trauma, or otherwise, regardless of whether it was sabotage or accidental.
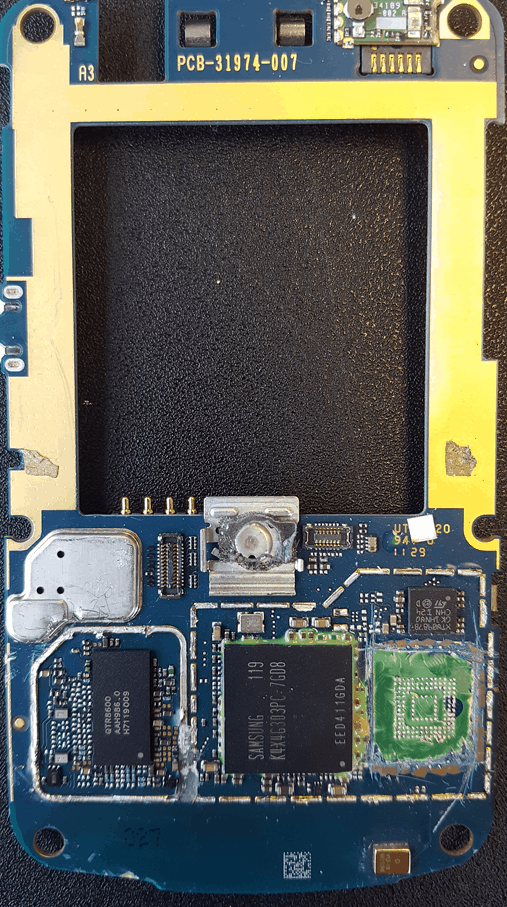
By performing a chip-off on the device, our examiners are able to access the NAND flash memory directly and perform a manual dump of the data. This can involve intricate physical work and soldering on the device before accessing the data, in addition to sometimes having to piecing together the chaotic jumble of data that is recovered. It would certainly be nice if everything came out clean on the other side, but the potential difficulty of the work is one of the reasons we take pride in our digital forensics experts.
Expert Testimony
While the physical and logical analysis of a device is important for a digital forensics case, expert testimony in a court of law is often even more important. Technical confusion can occur if the data is not clearly communicated to the jury, attorneys, and judge, which in some cases can invite the perception of reasonable doubt to enter a case.
Fortunately for our clients, the Gillware team has experience in a court of law and may provide expert testimony services when necessary. Whether that is to analyze an opponent’s arguments and data or to communicate the results of our own forensics work, Gillware is the right choice for your BlackBerry forensics case.
Use Gillware for Your BlackBerry Forensics Case
With our world-class digital forensics experts and the right tools to handle even the most difficult cases, use us for all your BlackBerry forensics needs.

